
Almost 2,000 hacked WordPress sites now display fake NFT and discount pop-ups to trick visitors into connecting their wallets to crypto drainers that automatically steal funds.
Website security firm Sucuri disclosed last month that hackers had compromised approximately 1,000 WordPress sites to promote crypto drainers, which they promoted via malvertising and YouTube videos.
It is believed that the threat actors were unsuccessful with their original campaign and began deploying news scripts on the compromised sites to turn visitors' web browsers into tools for brute-forcing the admin passwords at other sites.
These attacks involved a cluster of approximately 1,700 brute-forcing sites, including prominent examples like Ecuador's Association of Private Banks website. The goal was to build a large enough pool of sites that they could eventually monetize in a more extensive campaign.
According to cybersecurity researcher MalwareHunterTeam, the threat actors have now begun monetizing the pool of sites to display pop-ups promoting fake NFT offers and crypto discounts.
While it is unknown how many compromised sites are currently displaying these crypto drainers, an Urlscan search shows that over 2,000 compromised websites have been loading the malicious scripts over the past seven days.
Not all are generating the crypto pop-up scams at this time, but this could change at any moment.
Pop-ups lead to crypto drainers
The malicious scripts are loaded from the domain dynamic-linx[.]com, which is the same URL Sucuri saw last month.
This script will check for a specific cookie ("haw"), and if it does not exist, injects malicious scripts into the webpage, as shown below.

Source: BleepingComputer
The malicious code randomly displays a promotional pop-up, urging victims to connect their wallets to mint a promising NFT or to receive a discount on the website.

Source: BleepingComputer
BleepingComputer tested multiple sites hosting these scripts, and while there were initially some issues with the pop-ups not attempting to connect to wallets, they eventually started to work again.
When you click the connect button, the scripts will initially display native support for the MetaMask, Safe Wallet, Coinbase, Ledger, and Trust Wallet wallets. However, they also support 'WalletConnect,' which supports many other wallets, significantly expanding the targeting scope.
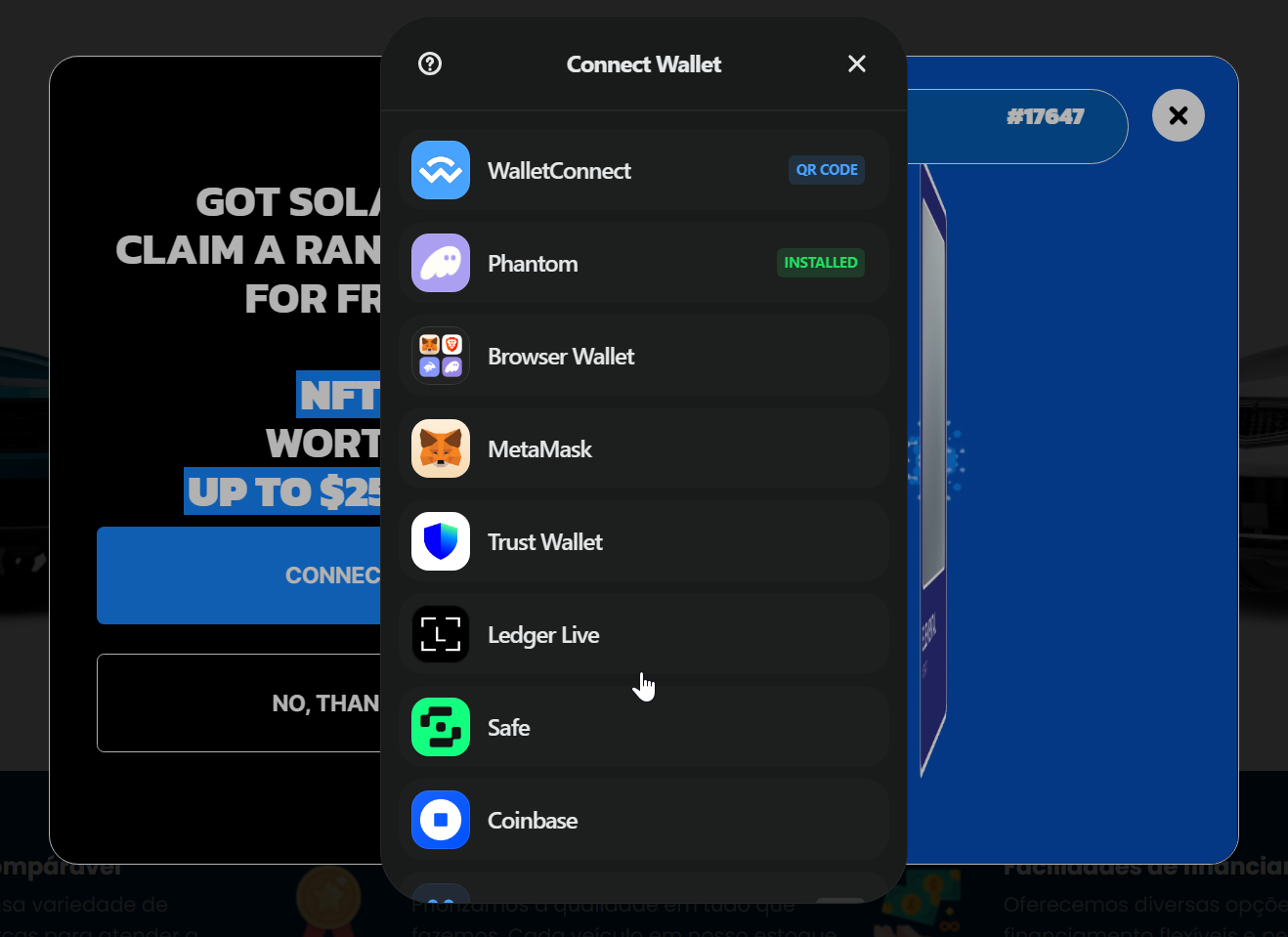
Source: BleepingComputer
Once a visitor connects the now Web3 site to their wallets, the crypto drainer will steal all the funds and NFTs in the account and send them to the threat actors.
It should be noted that MetaMask will display a warning when visiting websites infected with these malicious scripts.
Crypto drainers have become a massive problem for the cryptocurrency community, with threat actors hacking well-known X accounts and creating AI videos and malicious advertising to promote websites that utilize malicious scripts.
To avoid losing your digital assets to crypto drainer operators and other cyber criminals, only connect your wallet to trusted platforms.
Regardless of a website's established reputation, it is prudent to exercise caution with unexpected pop-up windows, especially when those don't align with a website's primary subject or design.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now